Security
Xbox One ‘Bliss’: Voltage Glitching, Boot Trust, and Unpatchable Hardware Reality
TLDR
SignalStack Tech Report · March 18, 2026 · Security / Hardware / Gaming
Why this is on SignalStack: we cover trust-anchor failures that are ROM-bounded—where software updates cannot restore assumptions hardware already shipped with.
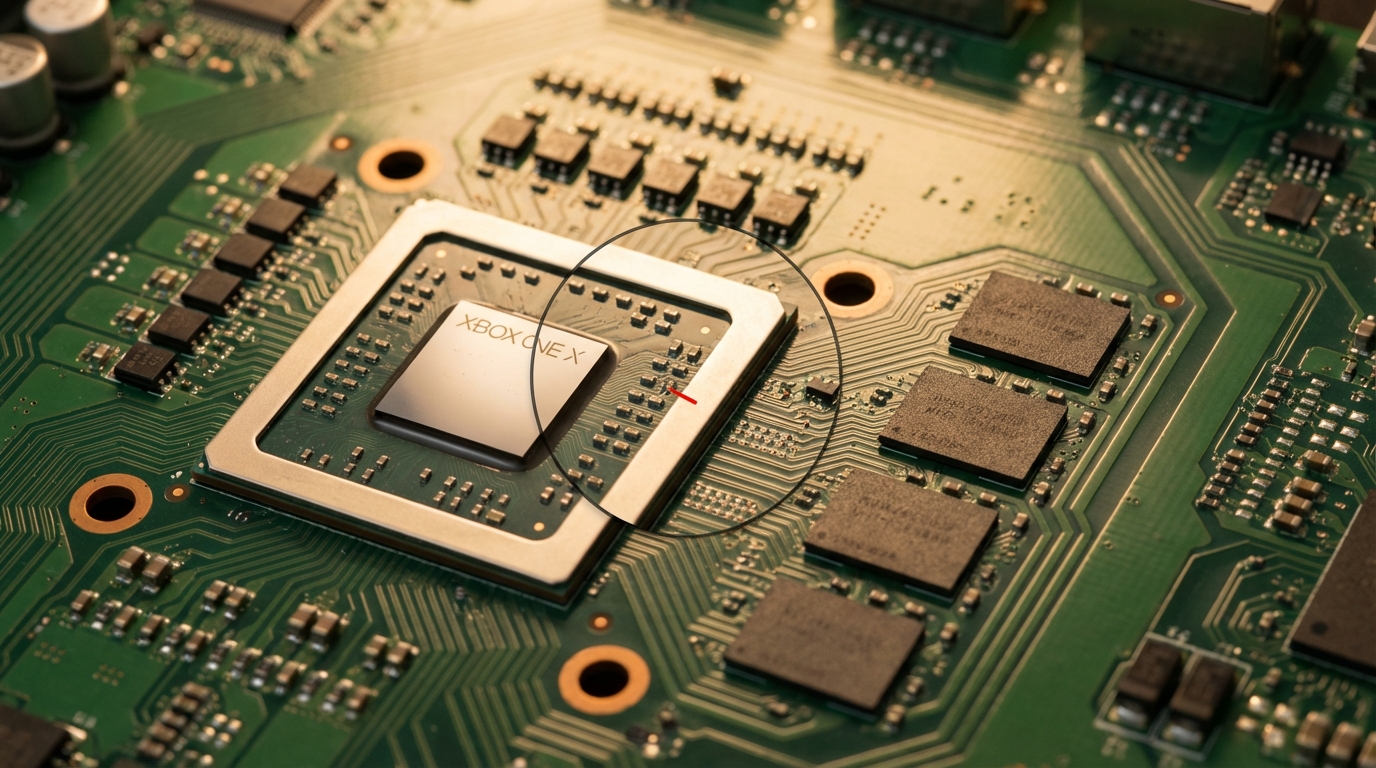
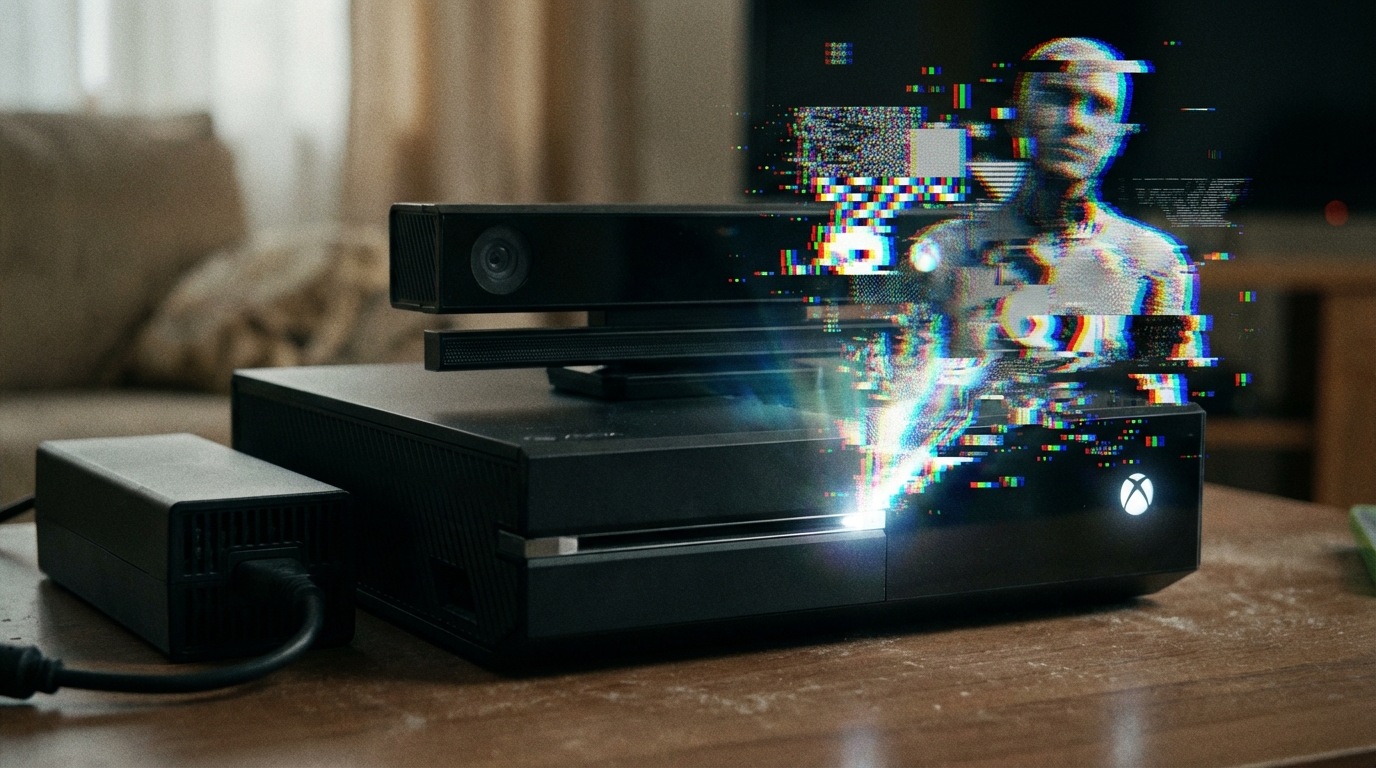
The original Xbox One, launched in 2013 and once considered exceptionally secure, has been compromised by a voltage-glitching technique known as “Bliss.”
The exploit enables unsigned code execution deep in the stack, including access paths to privileged components such as the hypervisor and security processor.
Because this is a hardware-level boot ROM issue, it is considered effectively unpatchable on already-shipped consoles.
What happened
After more than a decade of resisting major public jailbreaks, the original Xbox One has been hacked using a precise voltage glitching approach. The technique was presented publicly as “Bliss,” with the core idea being to induce carefully timed electrical faults during early boot so the device executes attacker-controlled code.In practical terms, this moves beyond surface-level exploits and targets a foundational trust point in the boot chain, which is why the result is described as “unpatchable” for existing hardware.
Why it matters
Long-lived consumer hardware tends to accumulate risk: even well-designed platforms eventually see researchers find paths around assumptions that held up for years. A boot-chain break changes the ceiling on what’s possible, opening the door to deeper inspection, preservation work, and experimentation that wasn’t previously feasible.That said, this is not a “click a link and you’re hacked” scenario. It’s a hardware procedure, and the difficulty of reliably reproducing it will likely limit it to researchers and highly technical enthusiasts.
Key details at a glance
| Topic | What’s reported | Why it’s constrained |
|---|---|---|
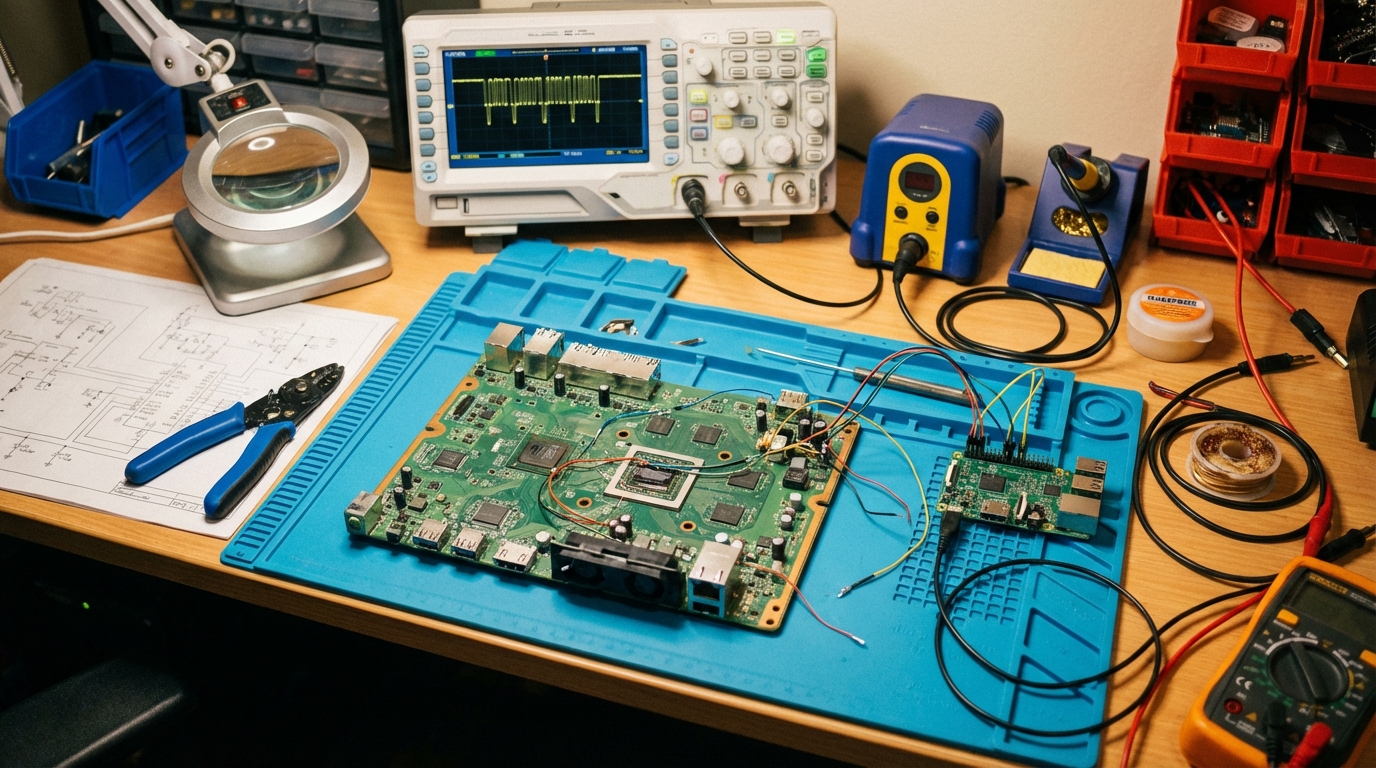
| Mechanism | Voltage glitching during early boot (“Bliss”) | Requires precise timing and hardware access—not a drive-by |
| Trust anchor | Boot ROM / early chain trust | Software updates cannot rewrite ROM on shipped silicon |
| Capability | Paths to privileged unsigned code once the chain breaks | Changes ceiling for research and abuse; not “instant mass exploit” |
| Skill & gear | Soldering, MCUs, tuning | Reproducibility stays in advanced hands |
| Scope | Original Xbox One generation emphasis | Newer revisions may differ—verify per hardware |
What to watch next
- Replication — Reliability, required hardware, and whether mod-chip-style automation becomes feasible.
- Community focus — Preservation and research tooling versus piracy-adjacent use cases.
- Vendor response — Mitigations on newer hardware if applicable; clarity on generation scope.
The SignalStack angle
What we are not doing: hyping “easy” jailbreaks. What we are doing: naming physical access plus glitching as the bar—still narrow, but foundational when ROM trust breaks.
1. Long-lived hardware accumulates risk
Platforms that resist public breaks for years still live under finite assumptions. SignalStack’s read: boot chains deserve red-team budget across the lifecycle, not launch week only.
2. Unpatchable is a policy and economics problem
When trust roots are immutable, incident response shifts to fleet replacement, content-protection posture, and ecosystem expectations.
Disclaimer: Details depend on primary research disclosures; verify before drawing legal conclusions about use.
FAQ
Q What is voltage glitching? A It is a hardware technique that deliberately perturbs the voltage supply at precise moments to induce faults and bypass checks.Q Can this be patched with a software update? A If the break truly hinges on immutable boot ROM behavior, software updates cannot fully remove the underlying vulnerability on existing devices.
Q Is this easy to do at home? A No. It requires hardware modification, tooling, and careful timing/tuning.